Index
Get the latest news right in your inbox
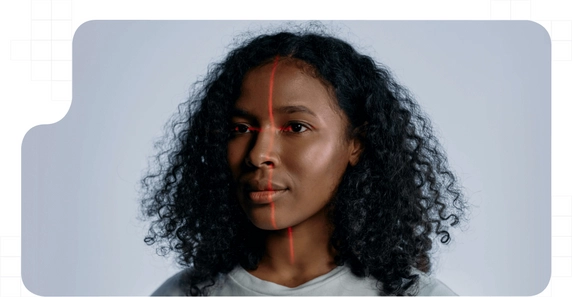
Face recognition techniques and applications are now, more than ever, part of our daily lives. This method of identifying people is a complete revolution in our economies and societies.
This technology is being used for a wide variety of use cases. While we might think that face biometrics is used solely and exclusively to grant access to cell phones and other computing devices, face recognition has a variety of applications.
Not everyone really knows what face recognition is and how it works, how the different systems interact with each other to compose a complete digitized record of our face and how the providers of this technology store this sensitive information.
Even if we don't fall for it, face recognition systems are found in more places than we think.
Basic definition of face recognition: what it is

Face recognition, by definition, is the ability to understand and remember a face, usually human. The technology that makes this possible is face recognition systems, which generally use tools based on artificial intelligence and machine learning algorithms.
In recent years, Face recognition is set as the fastest growing technology and the most widely used to verify the identity of users, customers or employees. Through image systems, video and audiovisual elements, a person's face is captured to generate a unique biometric pattern associated with a person's legal identity.
Face recognition is part of the so-called biometric techniques for identity verification since they measure a living organism and parameterize it to recognize it when it is present. In many cases, we can find face recognition included in the category of biometric security techniques, emerging as the first of them in order of relevance.
Practical applications and use of face recognition
Face recognition is used for a variety of purposes. Increasingly, this form of identity verification is used by many companies and institutions for traditional processes in a multitude of use cases.
This technology is applied to new and emerging areas as well as existing ones that are simplified and streamlined thanks to its integration. Among all the possible applications for face recognition, we can highlight the following:
- Identity verification for user registration (digital onboarding) and new customers for products and services that require identity confirmation (telephone operators, banking, finance, insurance...). Although it can be applied to any sector of activity with amazing results, these areas need it because of the sensitivity of the operations they must perform concerning their users.
- Knowing that the person is who they say they are is crucial for remote relationships and the online environment. For this reason, face recognition is being used for internet access, login in apps or web platforms, database security, online procedures with public administration, etc.
- Keys, pins on physical keyboards and other access systems to facilities, enclosures, vehicles, offices, warehouses, workplaces, etc., are at risk of being lost or stolen. Therefore, facial biometrics is being applied for these cases with the simple installation of a camera at the entrance to grant access, even with different levels of permission, to people in the organization or company.
- In the HORECA and tourism sector, we can grant access at check-in in hotels, for airport security and apply face recognition in dozens of circumstances in the leisure, restaurant and hotel sectors.
- In physical stores, for example, face recognition systems have been implemented to avoid having to go to the cash register. Customers visit the store, put their purchases in their bag and can leave, after which their customer account is debited for the amount purchased.
- In the area of law enforcement and security, it can be used to search for missing persons, recognize persons committing criminal acts, night surveillance or even forensic analysis.
Face recognition stands out for its unobtrusive nature and the simple and inexpensive way to implement it in any use case. The possibilities are limitless and any industry can take advantage of this solution to streamline processes, lower costs and provide a smooth and differentiated experience to its users.
Driving growth and expansion
In the case of banking, financial services, insurance and related industries, there are even specific legal regulations governing the use of face recognition to comply with the AML policies to which they are subject because of their activity.
Thanks to the current regulatory framework and the correct implementation of these systems, companies in any industry, including those mentioned above, can perform online face recognition and expand into other markets to operate in them and obtain new customers in a simple way and without additional investment.
This technology has made it possible to transform the current economy and turn sustainable business models into scalable and highly productive ones with only minor modifications to some processes.
How facial recognition works
To understand how face recognition works we must know all the phases that take place during the recognition process. Although the whole process occurs in milliseconds, 10 procedures are carried out in record time thanks to the advancement of technology.
Broadly speaking, and in a simplified manner, the phases of the face recognition process generally run as follows:
- Unidentified person: A person not identified by a face recognition system is about to be identified.
- Startup of audiovisual capture systems: The camera, infrared sensors and any hardware devices involved in data extraction is started and prepared to collect and measure information.
- Acquisition of images, video, depth data, infrared, other measurements and/or sound: The software starts receiving information from all available sources.
- Face location: The subject must fit his or her face in the frame visible to the camera.
- Face detection: The software works to detect the face, its depth, and differentiate it from the background and other elements of the scene.
- Conditioning and normalization: The area to be recorded is defined and the facial features that will make up the biometric pattern to be generated are parameterized.
- Feature extraction: Once the geometric transformations have been coupled and the rules have been established, the specific cast of the person being identified is extracted.
- DB recognition and comparison algorithm: The extracted vectors are compared with existing databases. If there is no pattern with a similarity percentage above the reference frame, the person is not previously registered in the system.
- Information storage: The created vector is stored in the database.
- Identified Person: The stored vector is linked to the identity data of a natural person.
- Authentication of the identified person: Here, the face recognition would have been completed. After that, the system can now recognize and authenticate the user in step 8 to grant access to products, services or facilities.
The effectiveness of face recognition is, in the most powerful systems, tested and certified. Like all advances in science and engineering, it responds to hit and miss rates and, fortunately, there are solid and proven face recognition solutions.
It should be noted that, of all the biometric identification methods (fingerprint, voice recognition, iris recognition, etc.), face biometrics is emerging as the most robust and, therefore, the most widespread system at present.
The security of facial recognition systems
Today, we can state without a doubt that face recognition is a mature, advanced and error-proof technology. As early as 2006, in the Face Recognition Grand Challenge (FRGC), the evaluation of the latest facial recognition algorithms was 10 times more robust and accurate than those used in 2002 and 100 times more accurate than those used in 1995.
Recently, there has been talked about the complications that can arise for face recognition systems after the emergence of deepfakes. Today, face recognition based on AI and machine learning is capable of surpassing the ability of humans, taking into account aspects that go unnoticed by our eyes.
Facial biometrics authentication
As we have seen, the main purpose of face recognition is to corroborate the identity of a person who is about to perform an action. First, if the person was not registered in the system, initial face recognition was performed to record and store his facial biometric data.
After verification and the creation of an account and credentials, we can ensure that the user who registered as a customer and contracted a product or service is who they claimed to be.
This, which is increasingly being implemented in all industries, although with special attention to those with a high level of risks such as banking, insurance, investments and the like, is necessary to comply with established technical and regulatory requirements.
According to several studies, already in 2016 and in the United States alone, theft associated with identity fraud exceeded a value of $16 billion and affected more than 15 million users. Across the pond, taking the United Kingdom as an example, its fraud prevention organization put the number of phishing cases at more than 170,00.
Your role in the customer journey
In this sense, and given the current situation, identity fraud represents one of the most important risks faced by both companies and users. Not only in digital onboarding, but also in subsequent steps.
To give an illustrative example, the theft of online banking passwords to make online payments, bank transfers to other accounts or spy on monetary information is more common than it might seem. All of this is due to the lack of secure and robust strong authentication systems.
Security in the customer journey must be provided in each and every one of its phases, establishing anti-fraud controls and incorporating integral systems that form part of a whole and adapt to all the company's channels. Balancing security and experience would mean giving up fundamental parts of both.
Therefore, having holistic and powerful online face recognition software that integrates across all phases is crucial to ensure a seamless, cohesive and secure experience. Multi-factor authentication systems can dispense with passwords, combining, for example, facial biometrics with SMS OTP codes.
























