Index
Get the latest news right in your inbox
Identity verification is now often associated with access to mobile devices. While this use case is important and necessary, the identity verification process is crucial when performing sensitive operations and activities such as user registration or opening a bank account.
This term has become much more important in the online environment than in the face-to-face, since - in addition to the fact that identity fraud rates are higher in this area - it is more complex to certify the veracity of the information provided by a computerized system than by a human in a remote operation.
However, thanks to the new and pioneering online identity verification systems, this is turned upside down, being able to say without any qualms that, today, a high-tech digital identity verification system is able to perform an identification process in a more reliable way than a human.
What is identity verification?
We can define identity verification as the series of processes and controls carried out to ensure that a subject is who he/she claims to be. Identity verification is usually performed on individuals, but it can also be performed on legal entities, in this second case, we would be talking about KYB (Know Your Business).
The concept of identity is based on comparing, and this term is defined as the quality of being identical and unique, comparable to another, and distinguishable from it. That is to say, to find an exact correspondence between one element and another, having a series of unique features that are associated with a subject in a unique, irreplaceable, and unchangeable way.
Thus, identity verification methods deal with different ways of ensuring that the person who is performing an action or who wants to be an active subject within a procedure (giving consent, accepting terms, contracting a product or service, registering on a platform...) is who he/she claims to be and that, on the other hand, in processes performed remotely, he/she is a real person.
System types and methods to verify identity
There are many different methods for verifying the identity of a subject. The choice of identity verification method and factors is crucial to establishing a fraud prevention and risk management strategy associated with each use case.
In the face-to-face environment, the usual method is the verification of the identity document by an agent. Although this method is secure, it is far from the security provided by digital methods, which carry out much more exhaustive and error-free checks.
Below, we list a number of the most prominent online identity verification methods:
- Verification through credentials: Passwords, pins, or usernames are designed to be generated in such a way that only the user who has chosen them knows what they are. This, however, is flawed if it is not combined with other factors and there is a risk that someone else could steal them or they could be forgotten.
- Knowledge-Based Verification (KBA): This factor refers to questions asked in such a way that the user to be identified is the only one who could answer them correctly.
- Verification by OTP (One Time Password): This method transmits a unique code valid only for a few minutes to a device that only the user to be verified can access. This can be done through one or multiple channels (SMS, email, phone call, letter, push notification...).
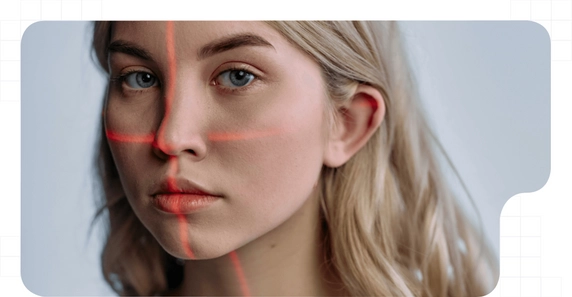
- Biometric verification: Use of the face (unique facial biometric pattern) and its cross-referencing with the image of the face shown on the ID card or other biometric factors such as voice, iris or fingerprint.
- Life detection verification: Generally part of biometric verification, it is especially important in online identity verification and involves extensive checks to verify that the biometric factors correspond to a person who is present in real-time in the process.
- Document verification: Checks the data and integrity of an identity document with advanced controls.
Verification of multiple factors:
In online identity verification, security depends on the system used and the factors chosen. It is best to combine at least two of the above factors. In this way, any attempt at identity fraud will be avoided and the greatest possible guarantee will be provided for a transaction to be carried out.
The combination of several of these factors results in the well-known KYC (Know Your Customer) process. This term is used in all industries, but especially in the financial, banking, insurance, investment, and related sectors.
Verifying the identity of users in KYC
Identity verification takes place in many sectors and areas of activity and is necessary for many use cases. However, there are certain industries that, due to sectorial regulations and both state and international laws, are obliged to establish identity verification procedures under a series of very specific technical standards.
On many occasions, the KYC and identity verification concepts are intermingled, being for many people the same thing. However, this is not the case. While identity verification is the concrete process of verifying and identifying a person, KYC not only includes this verification but also adds other steps to end up incorporating and registering a user within a company or platform, turning him into a customer.
Read this in-depth article for more details on the Know Your Customer (KYC) process.
The KYC process consists of a series of steps whereby a person is certified to be who they say they are and their identity is recorded in a database. The combination of several factors, namely facial biometric verification and identity document validation, along with data collection make up the Know Your Customer process, which is part of the broader digital onboarding.
Verification of identity documents
Identity document verification is another way to verify a customer's identity and is part of the Know Your Customer process.
In our societies, the basic form of identification of persons is based on identity documents issued by official bodies. In this sense, verification confirms that the person holding an identity document is the legitimate owner of that document.
Regarding face-to-face identification, it is well known that one of the main efforts of those who commit identity fraud is the forgery of documents. And not only the forgery but also the duplication of them illegitimately.
This process plays a crucial role in identity verification checks. Certifying the legitimacy of a driving license, national identification document (ID card), passport or official identification card is a complex task that must be carried out thoroughly.
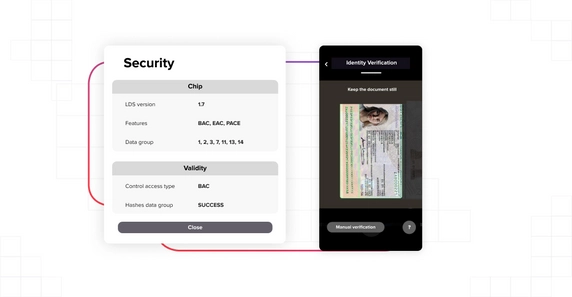
Among the checks performed, we can highlight the capture, extraction, analysis, and comparison of both the document data and the document itself: hologram, integrity, type of material, watermarks, elements in the right position, fonts, and typographies, spacing, corners...
We already advanced at the beginning of this article that digital systems have more resources to perform a correct and error-free identity verification than humans. The most advanced and secure systems, trained with millions of samples and powered by innovative artificial intelligence and machine learning solutions, have much lower error rates than humans, detecting minute alterations and performing a detailed analysis in seconds to identify a forged document without room for doubt.
Phases of the online identity verification process
Although there are different ways to perform an online identity verification process, not all of them meet the highest technical and regulatory standards. We can talk about selfie verification, video conference verification or streaming video identity verification.
Among these, the most agile, convenient, secure, adapted and supported by the rules and regulations to have the best legal guarantees is the streaming video identification. This method, which combines several factors, runs, in the best solutions, as follows:
- The user enters his data and registers and verifies his communication channels.
- Show an official identity document on both sides.
- The identity verification system reads, extracts, stores and verifies document data through OCR and performs veracity, integrity, and validity checks.
- The user shows his face on camera and makes a gesture (specific head movement, smile, talk...).
- The system verifies the user's identity by extracting and storing a unique biometric facial pattern and cross-referencing it with the content of the ID card.
- The user is registered in the system and the online identity verification process is resolved.
Data in identity verification systems
The management of this data, how it is stored, and how it is subsequently used must be carried out meticulously and according to very specific rules. This is where cryptography and end-to-end blockchain technologies come into play to ensure that the data is collected and processed in accordance with the regulations governing identity verification.
Regulatory framework for identity verification

Identity verification must be applied in all industries to provide support and guarantees in any user-company relationship. However, there are certain rules that regulate their use and oblige certain companies and institutions to implement them in certain ways depending on the level of risk of the different operations and use cases derived from their activity.
The most noteworthy rules in relation to identity verification are:
- AML: Money laundering prevention standards are crucial for certain industries and have specified the methods of identity verification and how they should be carried out in such a way that they are capable of preventing money laundering and terrorist financing.
- eIDAS: This is the basic framework on which European standards are defined, and which is taken as a reference beyond Europe, for digital identity and the use of electronic signatures.
- Data protection: Data protection and privacy standards bring together the controls and procedures to be taken into account for processing, managing and storing the personal and private data of both individuals and companies. Here, the European standard RGPD stands out.
- SCA: As part of laws such as PSD2, the SCA (Strong Customer Authentication) sets out guidelines for properly authenticating users in a secure manner. This framework outlines 2FA or MFA (multi-factor authentication) strategies and supports their use.
To give an example, in the United Kingdom alone, during 2017, the national fraud prevention organization put the number of attempted identity fraud cases at more than 175,000. This is just a small appreciation to understand why identity verification systems are essential for any company to operate with peace of mind and guarantees.
























